Best NordLayer Alternatives for Secure Remote Access and DNS Security
Compare top NordLayer alternatives for secure remote access, Zero Trust, and DNS filtering. See where Control D fits for safer internet access and simpler policy management.
NordLayer is a standard choice in the business VPN and Zero Trust market. For many organizations, it works. It gives them a single secure remote access solution that combines VPN tunnels, zero trust network access, and central policy management in one place.
But for others, the friction builds quickly. The cost per user rises, the requirement to install software on every device creates headaches, and you often pay for features you never touch.
This guide examines the top NordLayer alternatives by category. It looks at NordLayer alternatives and competitors across SASE, VPN software, DNS filtering, and identity, so you can see where each tool fits.
We review which tools handle private app access, which focus on internet security, and where Control D fits as a high-performance DNS security layer. This will help you build a secure, practical stack for your team without guesswork.
Best Nordlayer Alternatives by Category and How We Chose the Alternatives
Before going into detail, it helps to get a quick overview of the field. For this guide, we drew on product documentation, customer feedback, and real deployments. Then, we grouped the tools by what they do rather than by rating alone, so you can match them to your main use case rather than a simple “top 10” list of competitors and alternatives.
Best NordLayer alternatives at a glance:
| Category | Recommended NordLayer Alternative | Why it Stands Out |
|---|---|---|
| Best overall NordLayer alternative for a full SASE-style stack | Perimeter 81 | Combines ZTNA, secure web gateway, firewall, and cloud management in one platform for remote users and sites. |
| Best DNS-based alternative for safer internet access | Control D | Strong DNS filtering, granular policies, and traffic redirection that work with many VPN and ZTNA tools. |
| Best enterprise web and internet security choice | Zscaler Internet Access | Cloud secure web gateway and firewall built for large organizations with many sites and remote users. |
| Best app-level zero trust option | Twingate | Focuses on app-level access to private resources instead of broad network-level VPN access. |
| Best lightweight VPN for small teams | Windscribe | Extremely affordable team pricing with easy shared static IPs and simple billing. |
| Best self-hosted VPN option | OpenVPN Access | Gives full control over VPN placement and routing for teams that want to run their own gateways. |
For the rest of this guide, we group these tools into four broad categories:
- DNS-Based alternatives for internet access security
- SASE and ZTNA alternatives
- Self-hosted VPN and access server options
- Lightweight VPN alternative tools for small teams
Why Nordlayer Users Start Looking at Alternatives
NordLayer combines remote access, zero trust network access (ZTNA), and policy control. It offers encrypted tunnels, multi-factor authentication (MFA), and detailed logging.
For many teams, this central approach works well. They get one vendor for secure access to company resources, integrated logging, and support rather than stitching together several smaller tools. Larger organizations that want one console for access management often stay with NordLayer for that reason.
Over time, many users reach a point where the tool feels heavier than necessary. Some teams simply want safer internet access for remote workers. Others need better DNS control, simpler policy management, or pricing that does not punish growth.
Based on public reviews and user feedback, common friction points include:
- Per-user pricing that rises fast as headcount grows.
- The five-user minimum excludes small teams or solo operations, pushing them toward more flexible options.
- Users report performance issues with NordLayer, including connection loss and complicated VPN configurations that hinder usability.
- Less control over DNS filtering than a specialist DNS platform.
- Admin portal is lacking advanced features, which limits its overall effectiveness and functionality.
- Expensive, especially considering the complexity of support and configurations.
- Frequent app updates disrupt end-users, while features like IP cycling or apps for devices such as Firestick remain absent.
If you mainly want safer internet access and DNS control for remote work and office networks, a DNS filtering platform such as Control D can handle that part of the job for many NordLayer users. If you need full zero trust access to cloud environments and internal apps, SASE and ZTNA platforms such as Perimeter 81 or Check Point Harmony SASE may better meet your needs.
If your team values a single vendor and is happy with the feature set and price, staying with NordLayer and adding a separate DNS tool on top can still be a sound option.
Let’s look at each category in more depth, then show how Control D fits as a DNS-based layer across these options.
DNS-Based Alternatives for Internet Access Security
DNS-based tools focus on internet access security rather than private tunnels. They handle queries from users and remote devices, apply policy, and return responses that block or redirect traffic. This sits in front of any VPN or ZTNA solution you choose.
DNS filtering is useful if you want to:
- Block malware, phishing, and risky content before connections start.
- Apply access controls by category, app, domain, country, or ASN.
- Keep policy consistent for users on and off corporate networks.
- Improve data protection without sending every packet through a full VPN and still create secure internet access for remote users.
DNS tools do not replace ZTNA for private apps. Instead, they complement it. For some NordLayer users, this tool replaces only the internet access and web protection slices of their NordLayer usage.
Control D: Granular Security and Traffic Control for Modern Stacks
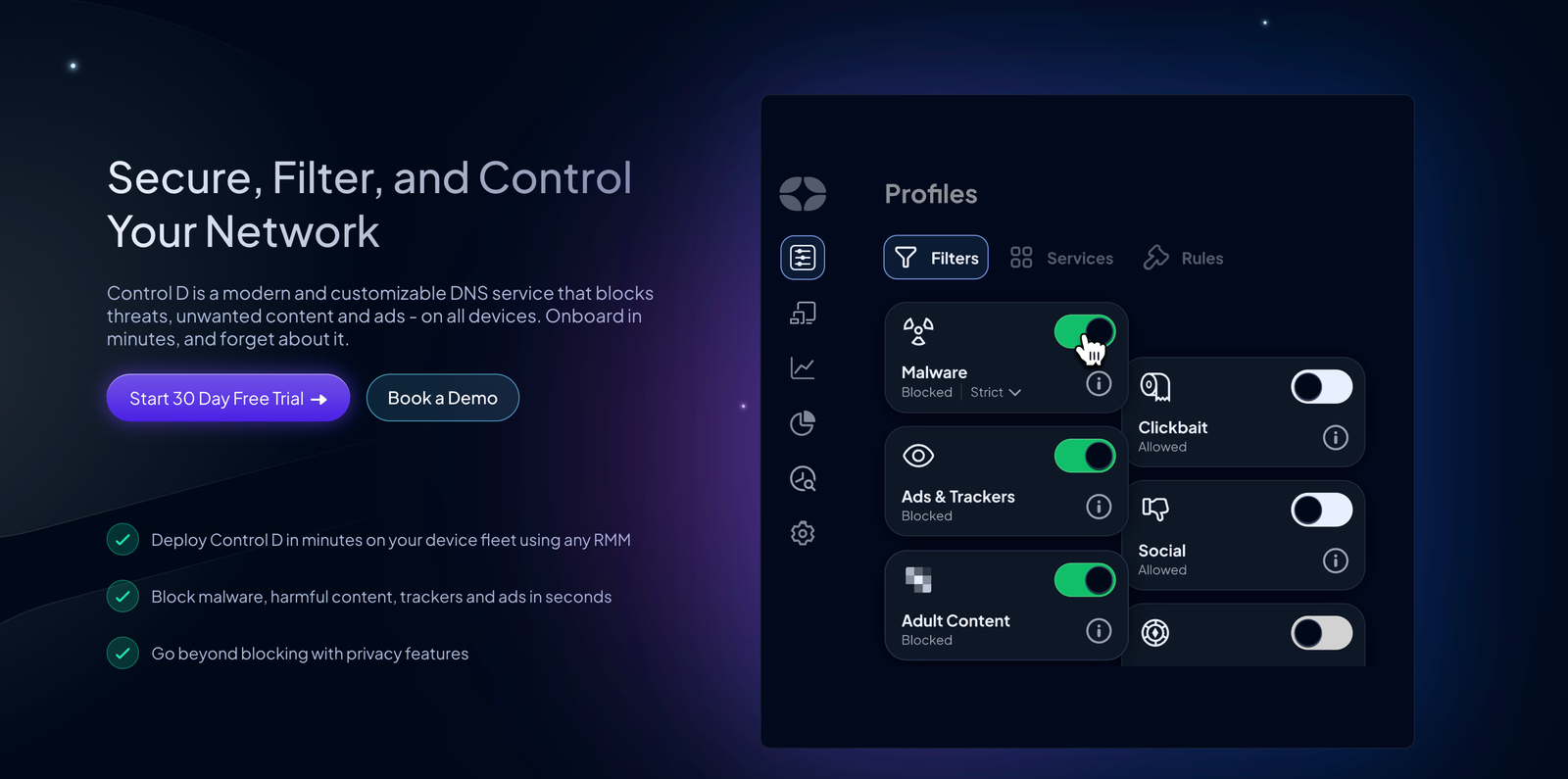
Control D is a DNS filtering platform designed for fine-grained control and instant policy updates. It allows IT teams to manage internet access across networks, devices, and roaming users from a single console.
Unlike a traditional VPN that tunnels everything, Control D inspects DNS queries. This means you get security and policy enforcement without the speed loss associated with encryption tunnels.
Key features include:
- Category-based rules for security and content.
- Service-based filters for popular apps and sites.
- Custom domain rules to block, allow, or redirect traffic.
- Policy scoping per network, user, device, or department.
- Traffic redirection through many exit locations for private internet access-style browsing.
- Detailed logs for network monitoring and threat detection.

Control D can sit in front of many different solutions. For example:
- Use Control D as the DNS layer for traditional VPNs, SASE tools, or private VPN setups.
- Point remote users and branch offices at Control D for consistent internet access policies.
- Use DNS policies to protect sensitive data from risky destinations across cloud environments.
This gives organizations a centralized management point for DNS security, independent of any single VPN vendor.
DNSFilter
DNSFilter is a cloud-based DNS security service aimed at IT teams and managed service providers that need threat blocking and reporting at the DNS layer across many networks.
- Where it improves on NordLayer: Strong security categories, threat feeds, and MSP-friendly reporting across many customer networks.
- Where it falls short: Less focus on traffic redirection and fine-grained service rules than Control D.
- Best for: Service providers that want brandable DNS security as part of their offering.
NextDNS
NextDNS is a privacy-focused DNS resolver that gives granular control per device and profile, often used by power users and smaller teams that want detailed tuning of DNS behavior and logging.
- Where it improves on NordLayer: Deep per-device control, privacy-first logging, and flexible profiles that suit power users.
- Where it falls short: Management at very large scale can be harder than with tools built for centralized control of thousands of users.
- Best for: Smaller environments and technical users who want to tune DNS behavior in detail.
Compared with these, Control D puts more weight on traffic redirection, service-level controls, and flexible policy scope across multiple networks and customers.
SASE and ZTNA Alternatives
If your main need is ZTNA and secure remote access into internal apps, you will likely compare SASE and ZTNA vendors. These platforms combine VPN capabilities with zero trust security ideas for users across many locations and cloud environments.
Perimeter 81
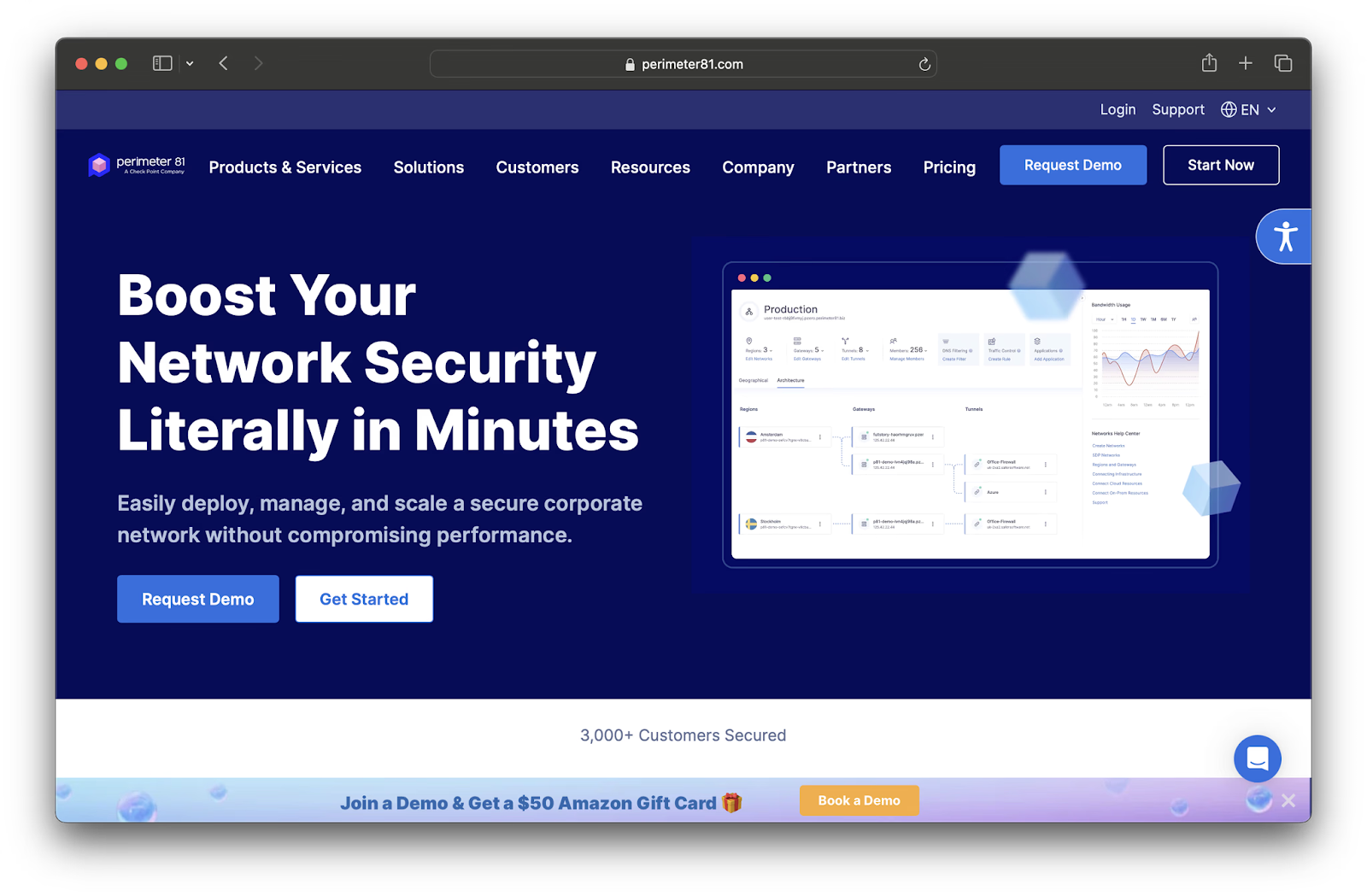
Perimeter 81, now part of the Check Point Harmony SASE portfolio, offers a cloud-managed platform for secure access to private and public resources. It combines ZTNA, a secure web gateway, a cloud firewall, and sometimes SD-WAN features to give remote users safer internet access and private app access.
- Where it improves on NordLayer: Broader SASE focus with web, DNS, and app access in one place. It’s also a strong fit for distributed sites that need consistent policy management and centralized control.
- Where NordLayer or others still win: Small teams may find Perimeter 81 closer to enterprise plans than they need. In these cases, NordLayer can feel simpler for basic secure remote access with fewer moving parts.
- Best for: Organizations that want a cloud-managed SASE platform and are ready for a deeper rollout to their remote workforce.
Check Point Harmony SASE

Check Point Harmony SASE is pitched as a modern secure remote access solution that goes beyond traditional VPNs and aims to create extremely secure access between users and resources. It ties in closely with Check Point firewalls and endpoint protection.
- Where it improves on NordLayer: Tight integration with existing Check Point security features and endpoint protection. It also offers a strong policy engine for sensitive data in complex networks.
- Where NordLayer or others still win: Less attractive if you are not already invested in Check Point products. Smaller teams may find the learning curve higher than with simpler NordLayer alternatives.
- Best for: Enterprises that already use Check Point and want to extend that stack to remote access and SASE.
Zscaler Internet Access

Zscaler Internet Access is a cloud-based secure web gateway and cloud firewall that sits between users and the public internet.
- Where it improves on NordLayer: Strong focus on web security, inspection, and policy for large numbers of sites and users. It’s a mature platform for enterprise-grade performance and comprehensive threat protection for internet access.
- Where NordLayer or others still win: Smaller organizations may find Zscaler too heavy for simple secure remote access. NordLayer or lighter VPN tools can be easier to roll out for basic remote access needs.
- Best for: Large organizations that want one provider between users and the public internet with strong security features.
Twingate

Twingate provides zero trust access to private apps without traditional site-to-site VPNs.
- Where it improves on NordLayer: App-level access model that exposes fewer network surfaces. A modern client experience that suits remote users who move between networks.
- Where NordLayer or others still win: NordLayer and SASE tools can cover both private apps and internet access in a single console. That said, DNS filtering and web security still need separate tools when you use Twingate on its own.
- Best for: Teams that want app-level access to private resources instead of traditional network-level connectivity
Where Control D Fits Alongside SASE
If you choose a SASE or ZTNA solution as your main NordLayer replacement, Control D still has a role. For example:
- Use Control D as a DNS layer for guest networks, lab networks, or legacy sites that sit outside SASE tunnels.
- Apply stronger DNS filtering than the built-in resolver in some SASE consoles.
- Keep DNS policy independent from your SASE vendor, so you can change SASE tools later without rewriting DNS rules.
This structure gives your IT team more freedom when it comes to long-term network security decisions.
Self-hosted VPN and Access Server Options
Some organizations prefer self-hosted VPN software and access server products. These tools provide VPN tunnels and secure remote access without a full SASE framework. Common choices include OpenVPN and IPsec gateways such as StrongSwan.
OpenVPN Access Server
OpenVPN Access Server is a self-hosted VPN platform that runs on your own servers or cloud instances.
- Where it improves on NordLayer: Gives you direct control over where VPN gateways live and how they connect to your networks. Fits teams that want a widely supported VPN protocol that many devices and firewalls already understand.
- Where NordLayer or others still win: NordLayer and SASE tools bundle zero trust policies, device checks, and web security into one managed service. Self-hosting brings patching, monitoring, and capacity planning back into your IT team's hands.
- Best for: Organizations that want mature VPN software with full control over placement and integration
StrongSwan and other IPsec-based gateways
StrongSwan and related IPsec gateways support site-to-site and remote access VPNs using standard IPsec protocols.
- Where it improves on NordLayer: Works well for site-to-site links between data centres, offices, and cloud networks. It uses widely supported IPsec standards that many routers and firewalls already support.
- Where NordLayer or others still win: NordLayer and SASE platforms make it easier to manage large numbers of remote users and devices from a single console. IPsec gateways tend to focus on connectivity rather than DNS security, application-level access, or user-based policies.
- Best for: Organizations with network engineers who already run IPsec links and want to extend that model to remote access
Control D fits here as the DNS and policy layer on top. You can point all VPN subnets at Control D, then apply DNS filtering and access controls by network or group. That way, you add protection and visibility to traditional VPNs without rewriting your entire stack.
Lightweight VPN Alternative Tools for Small Teams
Small business networks and smaller teams often want something lighter than full SASE, yet more structured than consumer VPN products. This is where light business VPN alternatives like Windscribe and UTunnel come in.
Windscribe

Windscribe is widely known for its consumer VPN, but its ScribeForce offering is a hidden gem for small businesses that need simple, shared team access without enterprise complexity.
- Where it improves on NordLayer: It is extremely cost-effective (often starting around $3/user) and offers a shared static IP feature that is much easier to manage than NordLayer’s dedicated gateways. It includes team management and centralized billing without forcing you into a heavy sales contract.
- Where NordLayer or others still win: NordLayer offers advanced network segmentation features that larger enterprises require.
- Best for: Small teams and startups that need a shared static IP for whitelisting (e.g., locking down WordPress admin or AWS access) but want to keep costs to a minimum.
Windscribe and Control D are highly compatible. You can easily configure Windscribe’s Flexible DNS settings to use Control D DoH/DoT resolvers, giving you a secure VPN tunnel with Control D’s advanced filtering inside it.
UTunnel
UTunnel helps teams create managed VPN servers in chosen regions or cloud environments, without having to run all the infrastructure manually.
- Where it improves on NordLayer: Clear control over where VPN gateways run and which cloud providers host them. Fits teams that want a private VPN footprint with a straightforward management layer. It suits simple site links and remote access use cases where full SASE would be overkill.
- Where NordLayer or others still win: NordLayer and SASE tools provide integrated DNS filtering, web security, and user-based policies that sit on top of connectivity. UTunnel leaves DNS filtering, threat detection, and some access controls to other tools in your stack.
- Best for: Small teams that want to stand up VPN servers quickly in their preferred regions and then rely on a DNS security layer, such as Control D, to block phishing, malware, and risky destinations.
How to Choose the Right NordLayer Alternative
NordLayer alternatives and competitors cover a wide range of use cases. A clear choice starts with your primary problem, not with vendor names.
Step 1: Identify your main use case
Look at how teams actually use NordLayer in your environment. Common patterns include:
- Secure remote access into internal apps and networks for a remote workforce and contractors.
- Zero trust network access to private environments across multiple locations.
- Secure internet access, data protection, and threat detection for remote users on any network.
- A mix of all three, with central policy management for different departments.
If secure remote access to private environments is the main goal, focus on SASE, Secure Service Edge (SSE), or ZTNA solution vendors. If safer internet access and a DNS policy for remote work are the main goals, focus on DNS filtering and secure web gateway tools. If you only need simple tunnels between users and fixed private networks, traditional business VPNs and access server products may be enough.
Step 2: Map Out Decision Criteria
Once you know your main use case, look at concrete factors. Key areas to compare include:
- Access Model: Does the tool focus on ZTNA, remote access through VPN tunnels, DNS-based control, or a mix of these?
- Security Coverage: How strong are the security features for internet access, network monitoring, and threat detection? Can it give remote users comprehensive threat protection without adding too much latency?
- Policy and Access Controls: Can your IT team apply detailed access control policies based on user groups, device posture, network, or application? Does it give centralized control that scales across many networks and teams?
- Deployment Model: Do you need easy deployment for small teams, or can you handle a more complex initial deployment? Does the tool integrate with your identity provider, SIEM, and other tools?
- Data and DNS Control: Do you need fine-grained DNS filtering, service-level rules, and traffic steering? How does the tool handle logging, retention, and data protection, including where DNS and user data are stored?
- Scale and Pricing Plans: Does the tool suit small business budgets, or lean more toward enterprise plans? Are there entry-level tiers for small teams and clear enterprise plans for larger rollouts? Can you get custom pricing or predictable costs for many sites and users?
FAQ About NordLayer Alternatives
Are There Better Alternatives to NordVPN?
NordVPN focuses on consumer VPN use, private internet access, and streaming, while NordLayer targets businesses and organizations. Some businesses prefer a VPN alternative that offers ZTNA, SD-WAN, or full SASE features, such as Perimeter 81 or Check Point Harmony SASE. Others combine traditional VPNs with DNS-based security such as Control D. The “best” option depends on your mix of secure remote access, budget, and risk profile.
Is NordLayer a Good VPN?
NordLayer is more than a traditional VPN. It is a secure remote access solution that applies zero trust principles, including continuous verification, MFA, device posture checks, and detailed access control policies. That design gives organizations strong control over who can reach which company resources. At the same time, some smaller teams find the platform heavy and look for lighter alternatives for NordLayer, such as simple VPNs and DNS filtering tools.
What is the Difference Between NordPass and NordLayer?
NordPass is a password manager. It protects credentials, passkeys, and other data across user devices and browsers. NordLayer focuses on network security. It gives secure remote access, ZTNA, and a central policy for traffic between users and resources. In many organizations, NordPass protects secrets, while NordLayer or another ZTNA solution provides trust-based access to networks and services. These tools solve related but separate security problems.